Keystore
How it works?
keystore - is a file encrypted by a user's secret. It is used to store private keys from user's wallets.
There are different versions of keystore which have different workflow:
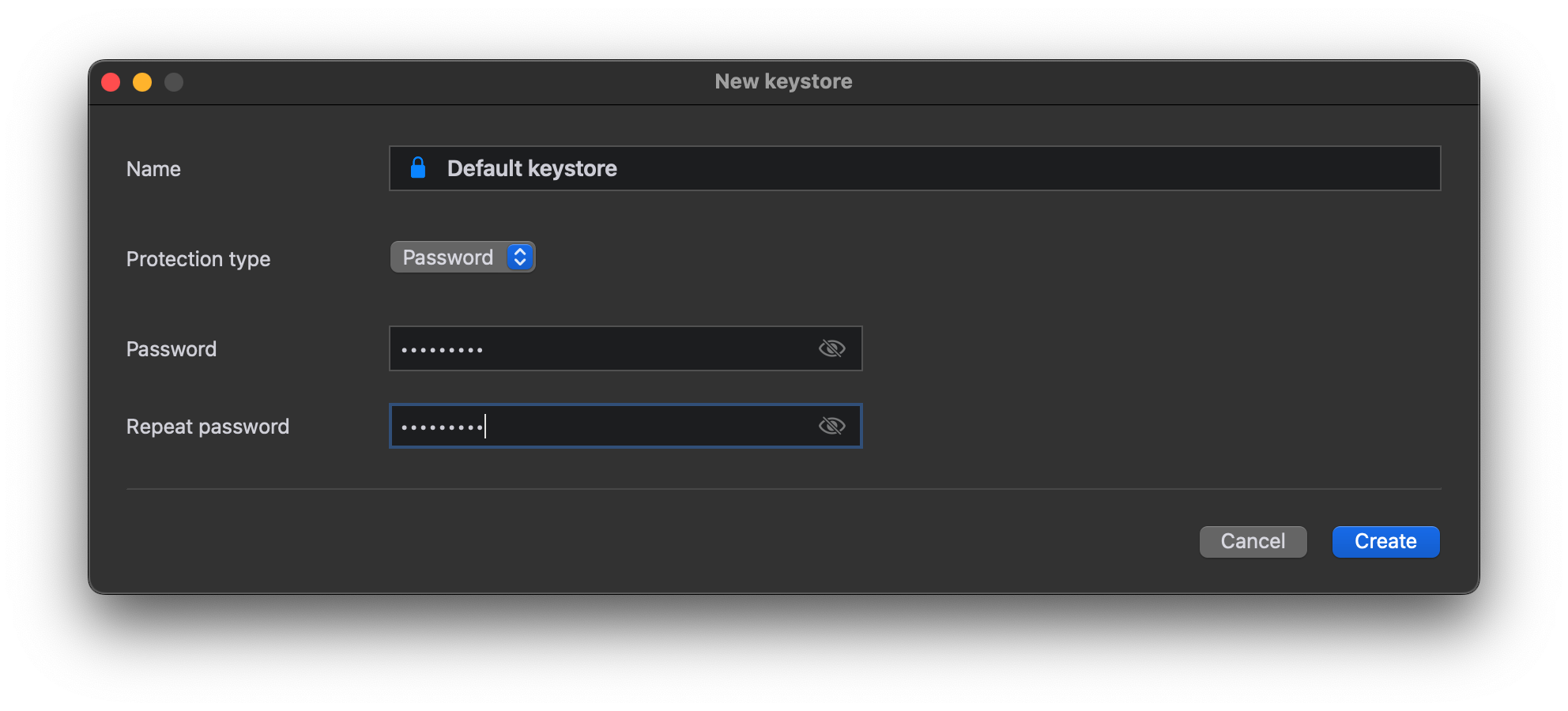
Password type keystore
Password type keystores encrypt only sensitive part of your data (e.g. wallet secret key). Public information are stored unencrypted (e.g. wallet address).
tons-gui
tons-interactive
- Open keystore (0:00)
- Create keystore (0:16)
- Backup keystore (0:42)
- Restore keystore (1:23)
tons
There are several options to work with a password:
- Runs a command and enter it through input
$ tons keystore new
Password []:
- Runs a command with a --password flag
$ tons keystore new --password admin123
Password []:
- Set up environment variable TONS_KEYSTORE_PASSWORD
$ export TONS_KEYSTORE_PASSWORD=admin123
$ tons keystore new
List all keystores in a tons.workdir folder
$ tons keystore list
dev.keystore
test.keystore
Create a new keystore
tons keystore new myNewKeystore --password MY_SECRET
Backup a keystore (password is used to export private keys)
tons keystore backup myNewKeystore ./myNewKeystore.backup --password MY_SECRET
Restore a keystore (password is used for a new keystore)
$ tons keystore restore keystoreFromBackup ./myOldKeystore.backup
Password []:
# to restore keystore from ton-cli's keystore add flag --from-ton-cli
$ tons keystore restore keystoreFromBackup ./ton-cli.backup --from-ton-cli
Password []:
Yubikey type keystore
YubiKey type keystores encrypt sensitive data, e.g. wallet secrets, with a private key that is stored on your device. Moreover, non-sensitive data, e.g. wallet address, is also encrypted by AES algorithm.
What is a YubiKey device?
The YubiKey is a hardware authentication device manufactured by Yubico to protect access to computers, networks, and online services that supports one-time passwords, public-key cryptography, and authentication.
You can buy the device on the official website.
IMPORTANT! tons requirements for a YubiKey device:
- Multi-protocol support
- Firmware version > 4.3.0
Example of the device that satisfies the requirements.
To set up your device, read the instructions on the Config page.
tons-interactive
- Create keystore (0:00)
- Touch YubiKey every time it starts blinking (when TOUCH_POLICY is set to ALWAYS) (0:15, 0:35)
- Other commands are the same as for password keystore, but requires YubiKey touch (if set to ALWAYS).
tons
Create new yubikey keystore
tons keystore new myNewYubiKeystore --keystore-type yubikey --pin MY_SECRET
Other commands are the same as for simple password keystore. But instead of --password you should use --pin option.